On
PHDays 2013 FastTrack I will speak about Dynamic detection of shell code in electronic documents
The past few years show frequent use of e-mail messages with electronic
documents containing exploits. Attackers use this technique to enlarge
botnets or to spy on the industrial secrets of an organization. The
report will describe dynamic detection of shellcode in electronic
documents without signature analysis to enhance security of employees
engaged in document flow. A zero-day vulnerability detected in
Yandex.Browser will be used to demonstrate how the software use can
decrease incident response time spent by the information security
service of a company.
My speech will be on Russian, but I'll try to create slides on English.
My speech based on
this article (in Russian)
We tested our programm on:
> 20 000 *.pdf files (was opened in Adobe Reader 9-11, Foxit Reader 3-6,
Google Chrome, Yandex.Browser)
> 10 000 *.doc, *.docx, *.rtf files (was opened in MS Word 2003, 2007, Libre Office 4.0)
OS Win XP, Win 7
We'he found:
Some APT attacks with some known CVE (CVE-2012-0158 and some else) for MS Word 2003, 2007
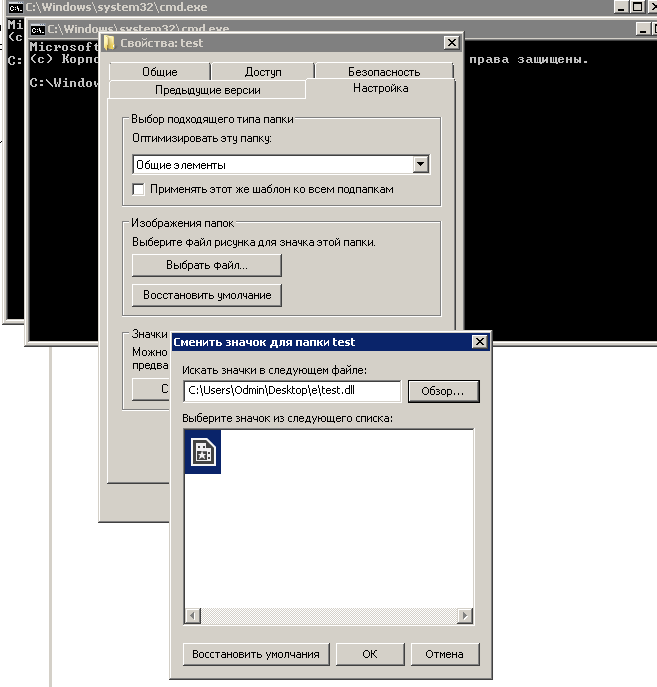
Vulnerability on Yandex.Browser (must fixed in latest version, but I didn't check it at this time)
Many crashes on many programs, that we still researching.
Original message on Russian